
11 March 2022
Cyberattacks are faster, smarter, and more relentless than ever, ranging from spear phishing and brute force to insider threats and cloud exploitation. Traditional tools can’t keep up.
Orange Cyberdefense Managed Threat Detection and Response gives you 24/7 protection with an intelligence-driven MDR service. By combining AI, automation, and expert analysts, we slash your Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR)—stopping threats before they cause damage.
Get proactive detection and response
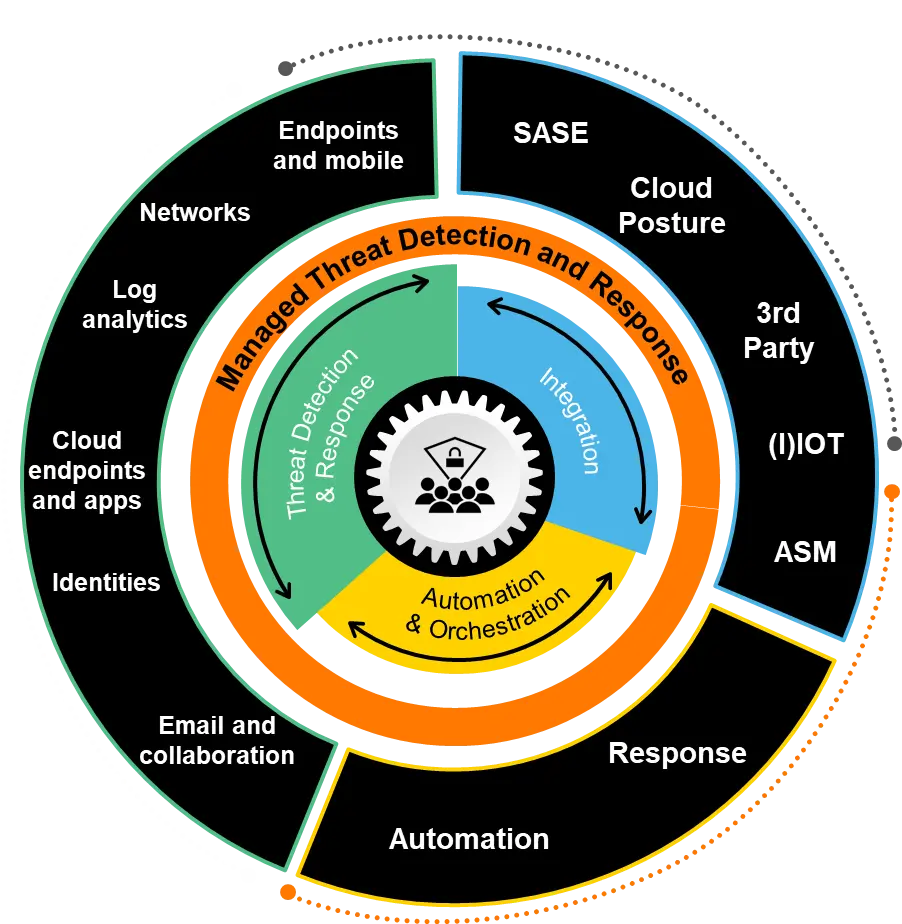
Our Managed Threat Detection and Response service unifies prevention, detection, investigation, and rapid response through our powerful Core Fusion Platform and AI. This enables us to:
Ingest & normalize telemetry across your entire environment
Enrich alerts with ThreatMap, our global Threat Intelligence
Uncover hard-to-detect threats through detection engineering and threat hunting
Automate triage to cut through the noise
Investigate & respond 24/7 with expert analysts
Contain incidents fast with decisive actions
Report & advise to keep you ahead of threats
Stay proactive. Stay protected. Transform your security.
Endpoints are at the center of how users interact with your business, which makes them a prime target for ransomware and other attacks. Our solution ensures endpoints are continuously monitored and protected to stop threats before they spread.
Monitor your key business systems: Collaboration tools, networks, and applications keep your business connected, but they can also be exploited as entry points by attackers. Managed Threat Detection defends these systems and prevents them from becoming a backdoor for cybercriminals.
Cloud services drive agility and scalability, but if compromised, that agility can be turned against you. MDR secures your cloud environments to detect and contain threats before they impact operations.
Security doesn’t stop at the perimeter. Our service extends visibility to the external digital footprint of your business, helping you identify and mitigate risks that exist “outside” your traditional boundaries.
Cyber incidents are inevitable, but being prepared minimizes impact. Managed Threat Detection equips you with expert guidance, automation, and proven response processes to contain and remediate threats quickly.
A diverse service portfolio: meeting your all-around security needs — MDR, penetration testing, SASE, and more — delivered by seasoned experts and tailored to your business objectives, compliance requirements, and long-term strategy.
Intelligence-led: hybrid AI & human operations, 38–48% of our IOCs are unique compared to other sources.
Exposure aware & outcome driven: safeguarding your own digital assets and your interactions with your supply chain, reducing exposure, acting proactively, and containing threats before impact.
Global expertise, local delivery: 32 hubs worldwide, operations fully hosted in Europe, interacting in many languages, sovereignty guaranteed.
Proven MDR leader: 15+ years of MDR experience, strategic partner of Microsoft, Palo Alto, trusted by leading enterprises.
Customer-first approach: Dedicated Service Delivery Manager + tailored security roadmap. We provide you with a service tailored to your needs.
Market recognition: IDC Leader category in the 2024 IDC MarketScape for European MDR services + listed by Forrester as "Strong Performer" for MDR.

To support your business goals, we offer flexible engagement models—try-and-buy programs, loyalty incentives, and scalable billing—so you can adopt at your own pace
Our team of MDR experts is always ready to help.
Fill in the form to get in touch with us or to schedule a no-obligation MDR consultation.
