
24 December 2021
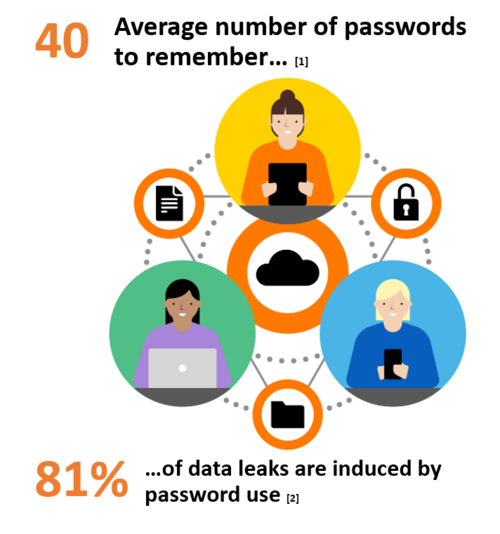
Nowadays, passwords appear to be more of a risk than an actual protection layer for the user. Passwords represent the key to secure all digital operations, yet have become a huge issue for users who have too many to manage, which often are lost or leaked. Indirectly, this complicates the work of the CISO, which must enhance secure access, strengthen security and simplify the life of users.
The challenge is now to own security solutions that allow users to protect the company’s data in the easiest possible way. Passwordless multi-factor authentication (MFA) combined with single-sign-on improves the security and reduces dramatically the risk.
[1] Cycloide report, 2018
[2] Helpnetsecurity, 2020

Hybrid environment support, single-sign-on (SSO), single pane of glass for user management
Granular access control with context based authentication (Zero Trust), wide range of step-up second factor
Fast deployment with full cloud-based architecture, easy migration from former strong authentication solutions
Access traceability and compliance reports in line with your Cloud migration requirements
Flexible Identity Authentication protects your resources with double authentication. To access them, your users generate a one-time password (OTP) using a PIN code and an authenticator: physical token, software, sms or grid.
Download datasheet
10 March 2022
